Walkthrough Challenge 0
We start by connecting to the terminal with the following command:
socat file:`tty`,rawer tcp:otp0.2023-bq.ctfcompetition.com:1337
We use the provided passwied
The terminal shows some kind of emai client. Navigating to the Sam Folder reveals a "Encrypted" Screen.

The challenge description privides us with a key:
VGhlIFZlbm9uYSBwcm9qZWN0IHdhcyBhIFVuaXRlZCBTdGF0ZXMgY291bnRlcmludGVsbGlnZW5jZSBwcm9ncmFtIGluaXRpYXRlZCBkdXJpbmcgV29ybGQgV2FyIElJLg==
We can decode this using base64 to obtain:
The Venona project was a United States counterintelligence program initiated during World War II.
If we press enter inside the terminal and paste the key, we can decode the message and obtain the flag.
The message is
Walkthrough Challenge 1
We start by connecting to the terminal with the following command:
socat file:`tty`,rawer tcp:otp1.2023-bq.ctfcompetition.com:1337
We use the provided passwied
Opening the folder
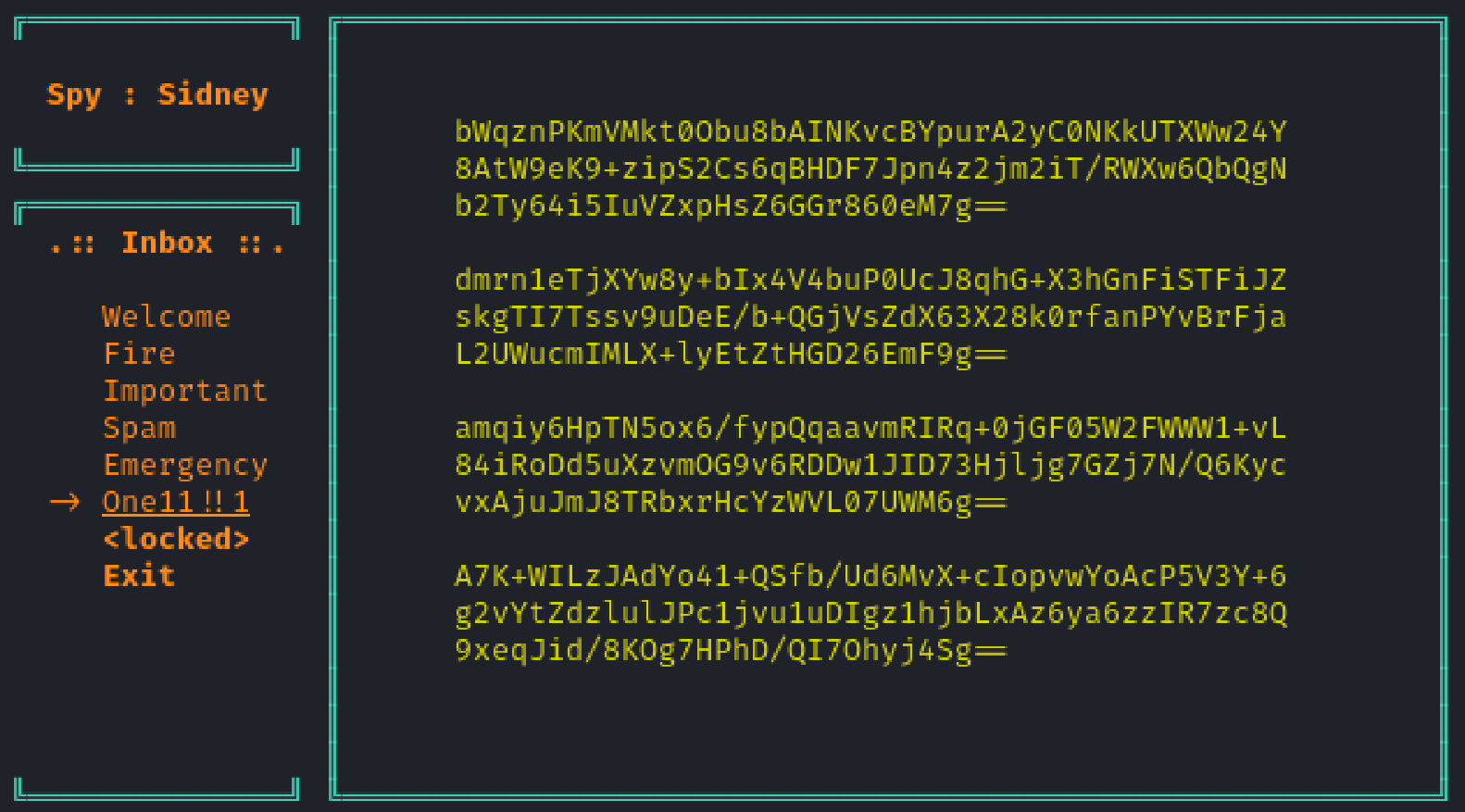
bWqznPKmVMkt0Obu8bAINKvcBYpurA2yC0NKkUTXWw24Y8AtW9eK9+zipS2Cs6qBHDF7Jpn4z2jm2iT/RWXw6QbQgNb2Ty64i5IuVZxpHsZ6GGr860eM7g==
dmrn1eTjXYw8y+bIx4V4buP0UcJ8qhG+X3hGnFiSTFiJZskgTI7Tssv9uDeE/b+QGjVsZdX63X28k0rfanPYvBrFjaL2UWucmIMLX+lyEtZtHGD26EmF9g==
amqiy6HpTN5ox6/fypQqaavmRIRq+0jGF05W2FWWW1+vL84iRoDd5uXzvmOG9v6RDDw1JID73Hjljg7GZj7N/Q6KycvxAjuJmJ8TRbxrHcYzWVL07UWM6g==
A7K+WILzJAdYo41+QSfb/Ud6MvX+cIopvwYoAcP5V3Y+6g2vYtZdzlulJPc1jvu1uDIgz1hjbLxAz6ya6zzIR7zc8Q9xeqJid/8KOg7HPhD/QI7Ohyj4Sg==
The challenge description hints "multi-time pad". This means that those messages are encrypted with one-time pad using the same key. This is a major security flaw, as it allows us to decrypt the messages.
We use MTP Interactive to decrypt the messages.
This tool requires us to convert the messages to hex format. We can use the following shell command to do so:
echo "<ENCRYPTED_MESSAGE>" | base64 -d | xxd -p
We write all the messages to a file and use the tool to decrypt them. The 4th message didn't decrypt properly, but we can decrypt the other 3 messages to obtain the flag:
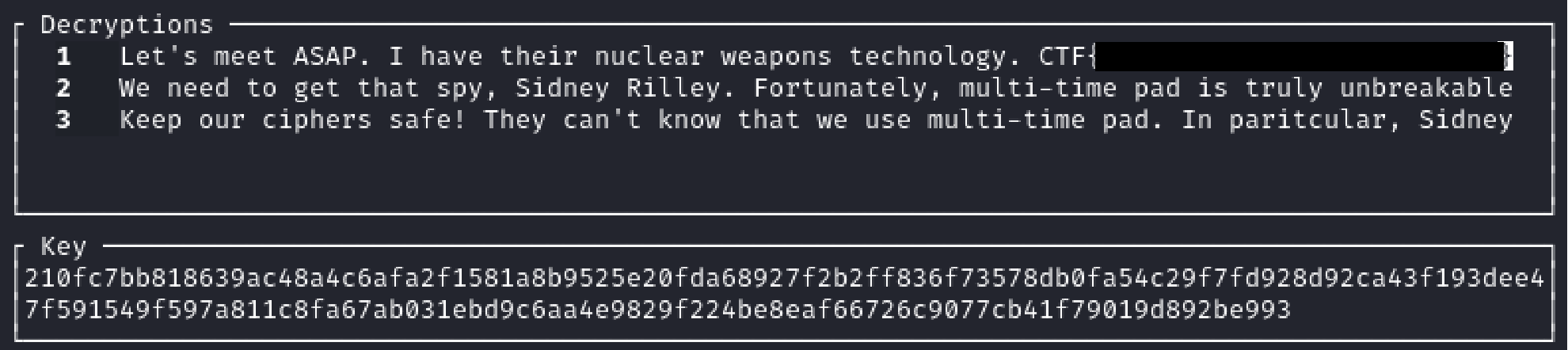
Let's meet ASAP. I have their nuclear weapons technology. CTF{XXXXXXXXXXXXXXXXXXXXXXXXX}
We need to get that spy, Sidney Rilley. Fortunately, multi-time pad is truly unbreakable
Keep our ciphers safe! They can't know that we use multi-time pad. In paritcular, Sidney
Walkthrough Challenge 2
We start by connecting to the terminal with the following command:
socat file:`tty`,rawer tcp:otp2.2023-bq.ctfcompetition.com:1337
We use the provided passwied
If we open the message
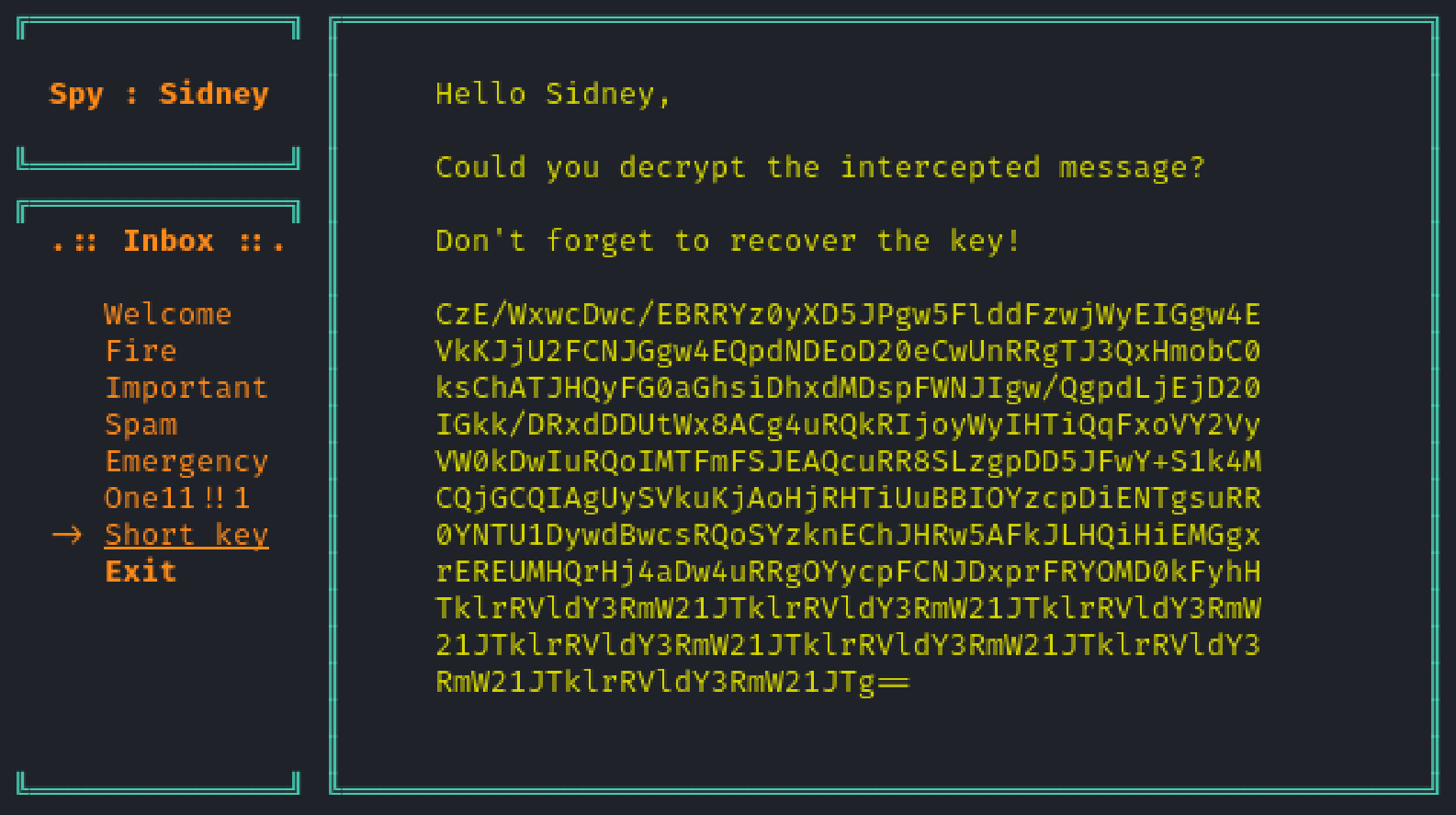
CzE/WxwcDwc/EBRRYz0yXD5JPgw5FlddFzwjWyEIGgw4EVkKJjU2FCNJGgw4EQpdNDEoD20eCwUnRRgTJ3QxHmobC0ksChATJHQyFG0aGhsiDhxdMDspFWNJIgw/QgpdLjEjD20IGkk/DRxdDDUtWx8ACg4uRQkRIjoyWyIHTiQqFxoVY2VyVW0kDwIuRQoIMTFmFSJEAQcuRR8SLzgpDD5JFwY+S1k4MCQjGCQIAgUySVkuKjAoHjRHTiUuBBIOYzcpDiENTgsuRR0YNTU1DywdBwcsRQoSYzknEChJHRw5AFkJLHQiHiEMGgxrEREUMHQrHj4aDw4uRRgOYycpFCNJDxprFRYOMD0kFyhHTklrRVldY3RmW21JTklrRVldY3RmW21JTklrRVldY3RmW21JTklrRVldY3RmW21JTklrRVldY3RmW21JTklrRVldY3RmW21JTklrRVldY3RmW21JTg==
Decoding this using
This looks like a Vigenère cipher.
We can assume that
If we assume that the message got filled with whitespaces at the end we can recover the key by shifting the characters back.
We can use the following python script to do so:
key = "ctf[mINIkEY]"
for c in key:
print(chr(ord(c) ^ 0x20), end="")
print()
We obtain the key and flag