
Walkthrough
We start by downloading the source files.
We are given a
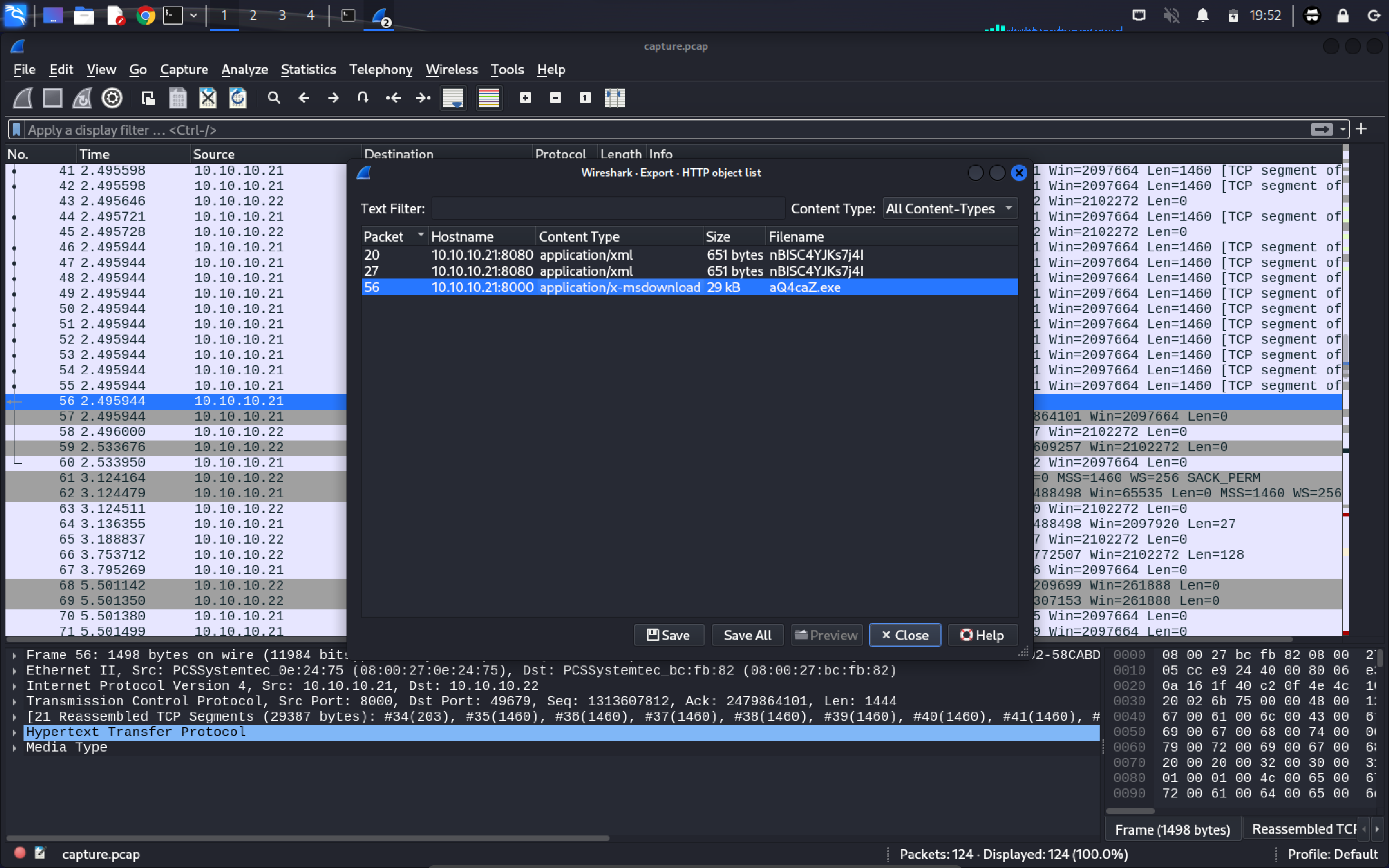
After looking at the packets for some time we notice a web request that downloads an executable file. We can download the file using the
To do that click on
We will now use the ILspy vscode extension to decompile the executable file.
After decompiling the file we can see that it has a function that encrypts and decrypts data. The executable looks like a control tool to remotely control the infected machines.
We find traffic in wireshark that looks like the communication with the control tool. You can find this here.
Unfortunately the traffic is encrypted, so we need to decrypt it. Fotunately we have the decompiled executable and can steal the decryption function from it. It uses
using System;
using System.Collections.Generic;
using System.IO;
using System.Net;
using System.Net.Sockets;
using System.Runtime.InteropServices;
using System.Security.Cryptography;
using System.Text;
using System.Threading;
public class HelloWorld
{
public static string Decrypt(string cipherText)
{
try
{
string encryptKey = "VYAemVeO3zUDTL6N62kVA";
byte[] array = Convert.FromBase64String(cipherText);
using (Aes aes = Aes.Create())
{
Rfc2898DeriveBytes rfc2898DeriveBytes = new Rfc2898DeriveBytes(encryptKey, new byte[13]
{
86, 101, 114, 121, 95, 83, 51, 99, 114, 51,
116, 95, 83
});
aes.Key = rfc2898DeriveBytes.GetBytes(32);
aes.IV = rfc2898DeriveBytes.GetBytes(16);
using MemoryStream memoryStream = new MemoryStream();
using (CryptoStream cryptoStream = new CryptoStream(memoryStream, aes.CreateDecryptor(), CryptoStreamMode.Write))
{
cryptoStream.Write(array, 0, array.Length);
cryptoStream.Close();
}
cipherText = Encoding.Default.GetString(memoryStream.ToArray());
}
return cipherText;
}
catch (Exception ex)
{
Console.WriteLine(ex.Message);
Console.WriteLine("Cipher Text: " + cipherText);
return "error";
}
}
public static void Main(string[] args)
{
Console.WriteLine(Decrypt("1BhuY4/niTopIBHAN6vvmQ=="));
}
}
We use this script to decrypt the traffic. You can find the decrypted traffic here.
This already contains two parts of the flag:
The last part is just
We can now put the three parts together to get the flag