Walkthrough
We start by downloading the old password checker.
If we run the binary we are prompted to enter a name and a password. We try to use the name "LosCapitan", which provided in the challenge description and a random password. The binary responds with
Let's open the binary in
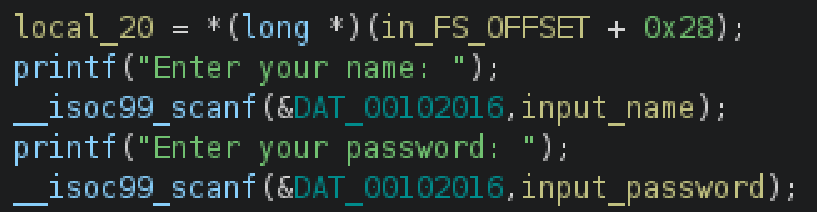
The binary reads the name and the password from the user.
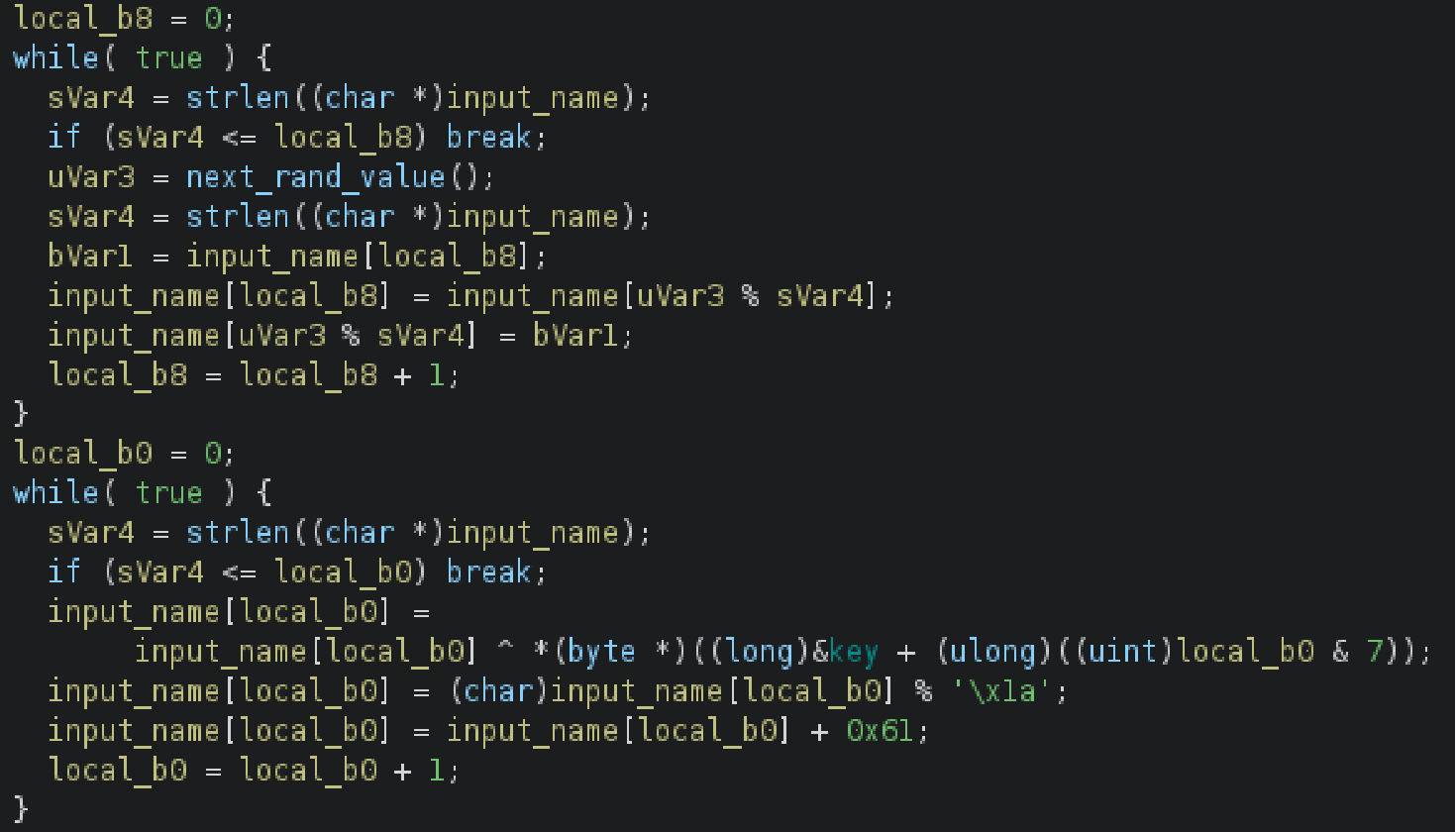
Then the binary does some calculations on the name:
Finally, the binary compares the calculated name with the provided password and prints
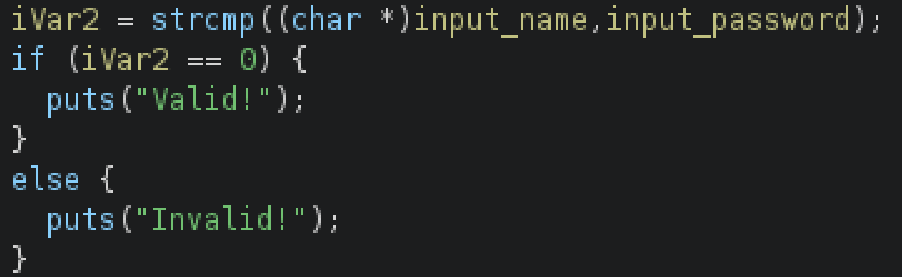
This suggests that the password is derived from the name. Because we don't want to reverse the calculations, we can use the binary to calculate the password for us. We do this opening the binary in
pwndbg> start
Temporary breakpoint 1 at 0x124e
Temporary breakpoint 1, 0x000055555555524e in main ()
pwndbg> b *main+0x24e
Breakpoint 2 at 0x555555555494
pwndbg> run
After setting the breakpoint we run the binary and provide the name "LosCapitan" and some random password. We then continue the execution until the breakpoint is hit. This reveals the correct password inside the
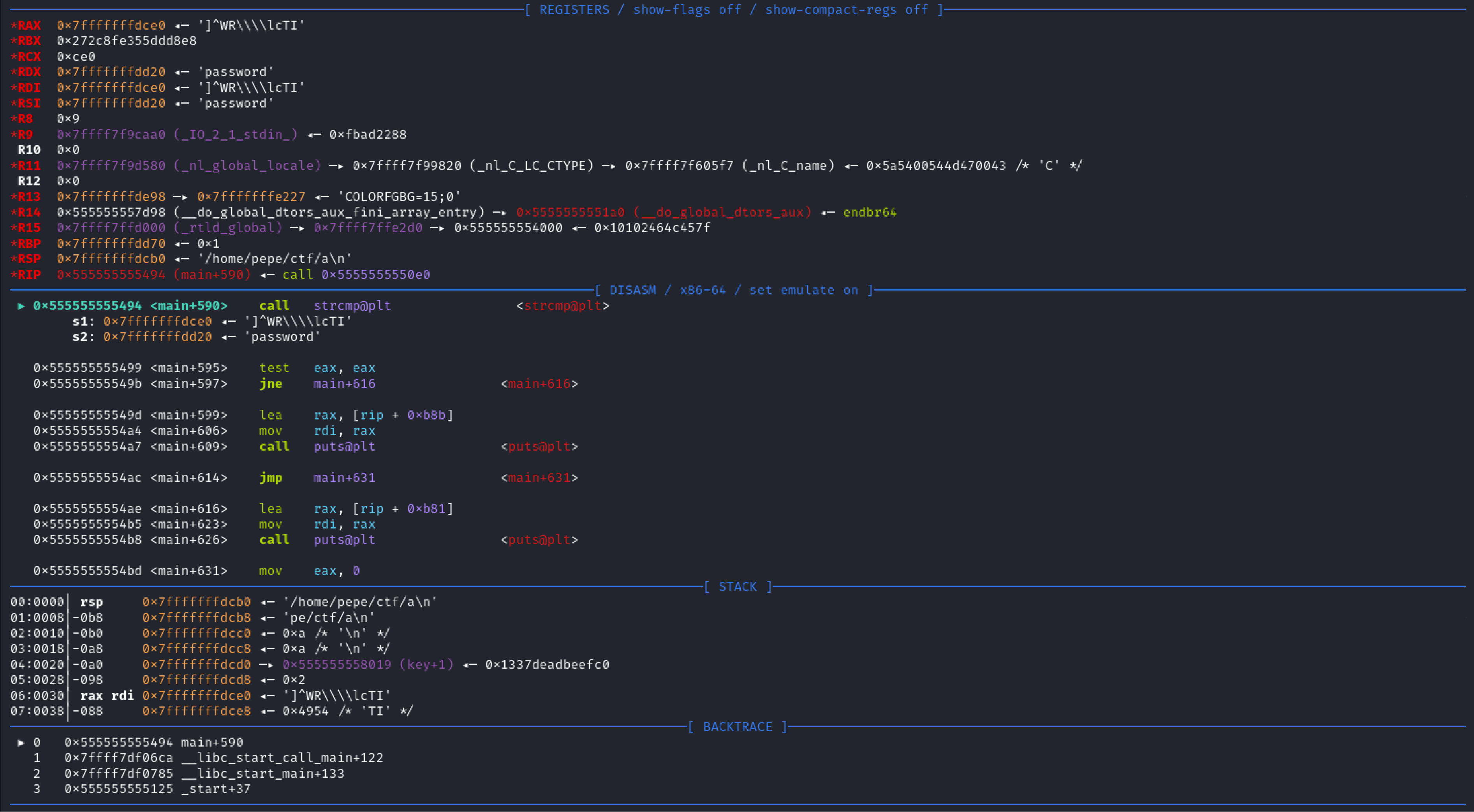
To get the flag we have to unescape the double backslashes inside the password and wrap it in